Expert Speak
How Hackers Are Finding Insiders on the Darknet

Check Point Research (CPR), the Threat Intelligence arm of Check Point Software Technologies Ltd., warns that it is not only hacking tools and threats or weapons, drugs and stolen personal information and login credentials that are traded in the dark corners of the internet but also where various insiders and hacker groups are continuously offering their services and cybercriminals looking for collaborators to help them attack organisations from the inside.
The Darknet is attractive to cybercriminals because of its near-perfect anonymity, making it an ideal space for finding collaborators and offering illegal employment opportunities. Many offers are targeted at insiders, those with knowledge of and access to sensitive systems who can help cybercriminals penetrate protected networks. While we can imagine that with the advancement of cyber tools, insider business will diminish – we observe that during the last two years, it has continued to flourish in the darknet.
Job offers on the darknet
“Cybercriminals often use specialised forums and marketplaces on the darknet to post job offers. These can attract tech-savvy users who are disenchanted with the traditional job market or are willing to go beyond the law for financial reward. Offers can range from hacking and data theft to malware deployment and ransomware campaigns. Hacker groups expect insiders to provide access to target systems, assist in overcoming security measures, and provide useful information for a successful attack. Or even attempt physical sabotage,” says Sergey Shykevich, Threat Intelligence Group Manager, Check Point Research.
Finding insiders
Insiders are valuable to cybercriminals because they have access to critical information and can weaken security measures from the inside. Cybercriminals often offer high financial rewards for cooperation and may even provide special training to maximize damage. For example, how to install malware or otherwise sabotage employers’ security systems. There are dozens of similar ads on the darknet. Often these are advertisements from Russia or the Commonwealth of Independent States (CIS).
Hiring an insider is expensive and dangerous, which is why cybercriminals target lucrative industries and large companies in these cases. For example, the financial, telecommunications or technology sectors are popular targets.
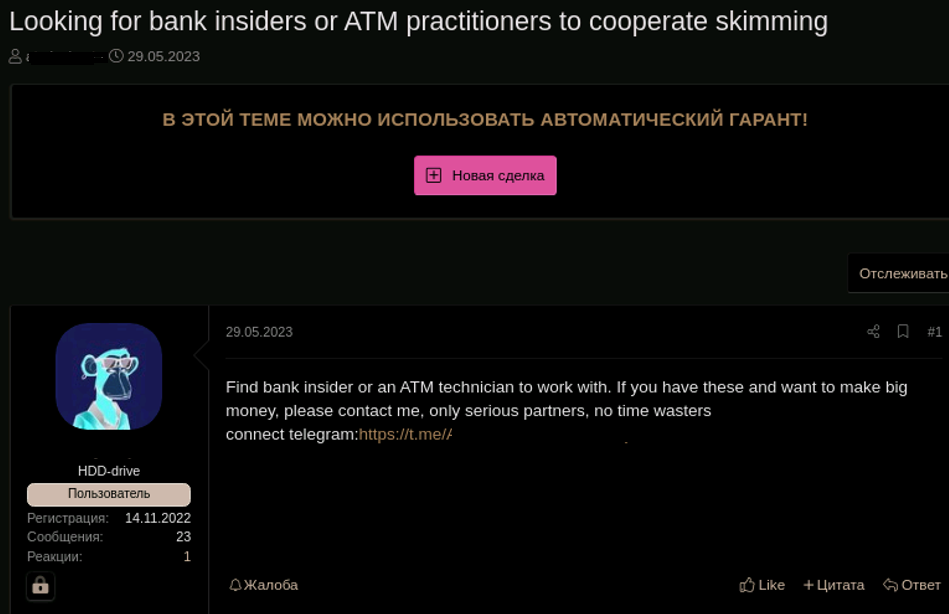
But it’s not just cybercriminals looking for collaborators on the darknet, insiders are also proactively offering their services. For example, an employee of a major mobile operator in Russia offered SIM card swapping and other illegal services. There are many similar advertisements also for the US telecommunication operators.
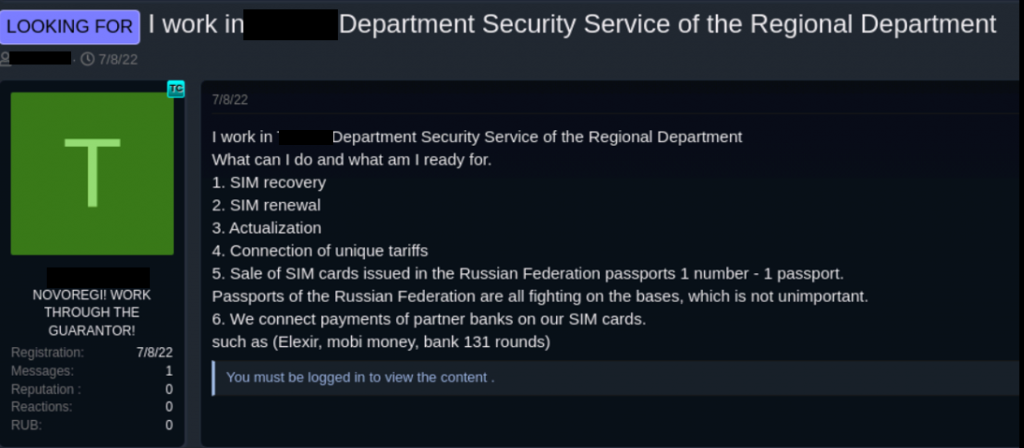
Insider service offers from the financial sector and the world of cryptocurrencies are also popular.
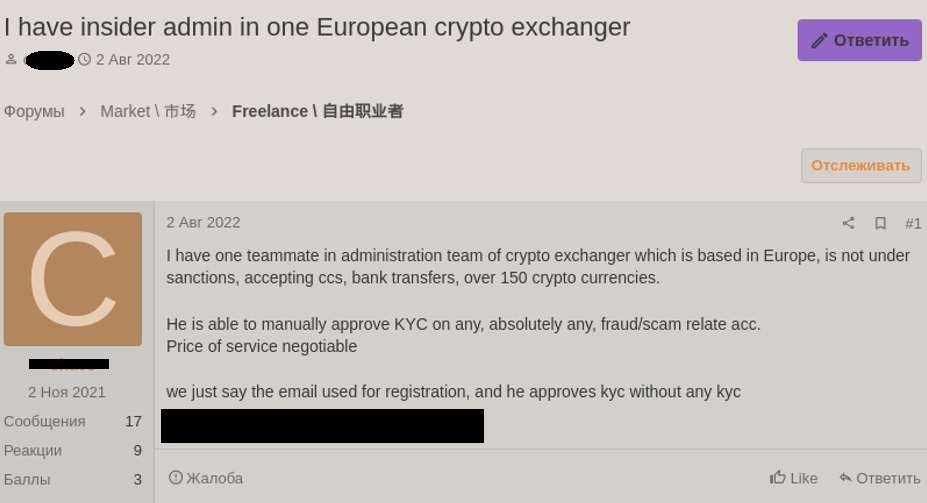
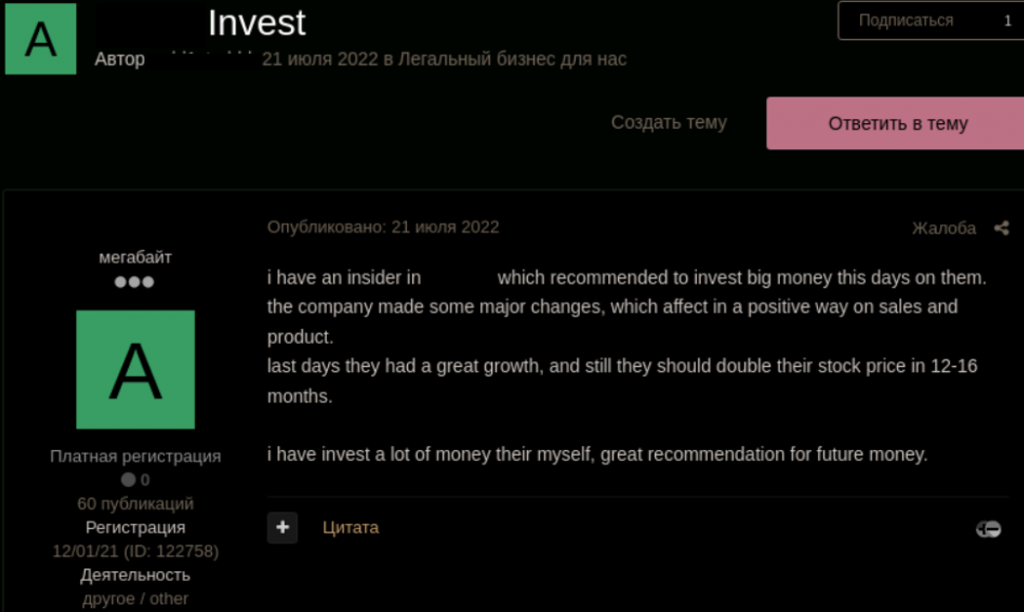
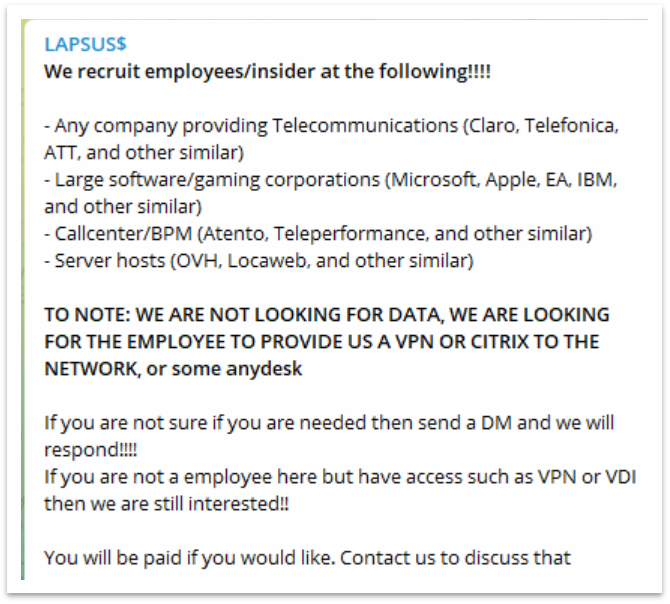
And the technology sector has traditionally faced the threat of insiders.
But no sector is exempt from risk, as the advert relating to the shoe and fashion trade shows.
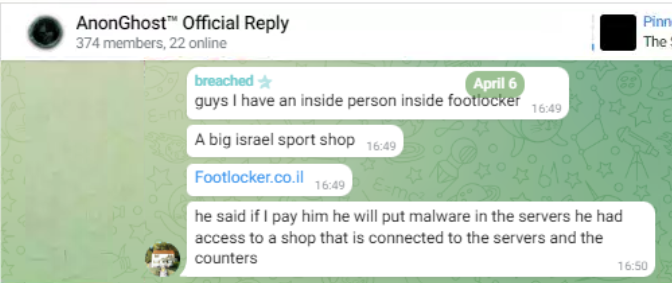
There are cybercrime organisations in Russia and Eastern Europe that monitor insider networks in various organisations. But some of them also offer their insiders who provide illegal or at least dubious services in other countries. One such insider is a hacker with the nickname Videntis.
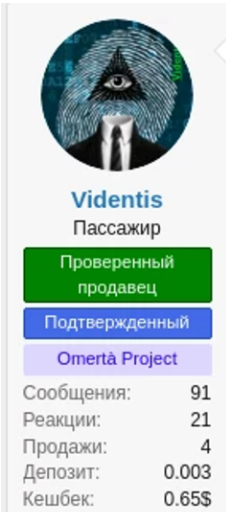
Videntis has a catalogue of over 11 pages offering insider-related services. Some of the services are very common, such as finding a mobile number for 2,500 rubles within 48 hours, listing all calls and SMS within 72 hours for 25,000 rubles, or forwarding all calls from a specific number for 19,000 rubles.
Other services involve specific Russian banks. For 8,000 rubles it is possible to find out a secret word within 72 hours or get a statement from any account for 9,000 rubles. For $900, a hacker promises to use his contacts to block any user’s WhatsApp, block a SIM card with any operator, or for $850, block any personal Instagram or TikTok account within 7-30 days. Some services are more versatile, such as confirming vaccinations abroad or creating health documents for travel.
A profitable deal for both parties
For insiders, working with cybercriminals is high risk; they can face criminal prosecution and loss of professional reputation. And there are rewards to match. However, for some, the main motivation may be revenge. The reward may be in the form of a direct payment or a share of the profits from the stolen data. In some cases, rewards may be contingent on the success of the attack or the amount of data recovered.
The infamous hacker group LAPSUS$, for example, sought an insider inside telco companies and offered a reward and low risk for both the insider and the hackers. Another group, in turn, offered $2,000-$5,000 to employees who had access to drivers at various food delivery services. But higher amounts, such as up to $100,000 to insiders at technology companies, are no exception. The impact of attacks involving insiders can be devastating. The Ponemon Institute’s “Cost of Insider Threats Global Report” reports that in 2021, the average cost per incident associated with insider activity will climb to $15.38 million.
Insiders can be employees, suppliers or employees of partner companies. In addition, their motives can vary from financial gain to revenge to political or ideological reasons. Collaboration between cybercriminals and insiders on the darknet poses a serious threat to companies’ data security and infrastructure.
This phenomenon requires the utmost attention and a proactive approach to security, including employee training, implementation of appropriate security policies, detection of suspicious behaviour, monitoring of the entire environment and regular audits. It is important to understand that prevention is key in the fight against cybercrime.
Artificial Intelligence
How AI is Reinventing Cybersecurity for the Automotive Industry

Written by Alain Penel, VP of Middle East, CIS & Turkey at Fortinet (more…)
Cyber Security
Positive Technologies Study Reveals Successful Cyberattacks Nett 5X Profits

Positive Technologies has released a study on the dark web market, analysing prices for illegal cybersecurity services and products, as well as the costs incurred by cybercriminals to carry out attacks. The most expensive type of malware is ransomware, with a median cost of $7,500. Zero-day exploits are particularly valuable, often being sold for millions of dollars. However, the net profit from a successful cyberattack can be five times the cost of organizing it.
Experts estimate that performing a popular phishing attack involving ransomware costs novice cybercriminals at least $20,000. First, hackers rent dedicated servers, subscribe to VPN services, and acquire other tools to build a secure and anonymous IT infrastructure to manage the attack. Attackers also need to acquire the source code of malicious software or subscribe to ready-to-use malware, as well as tools for infiltrating the victim’s system and evading detection by security measures. Moreover, cybercriminals can consult with seasoned experts, purchase access to targeted infrastructures and company data, and escalate privileges within a compromised system. Products and tools are readily available for purchase on the dark web, catering to beginners. The darknet also offers leaked malware along with detailed instructions, making it easier for novice cybercriminals to carry out attacks.
Malware is one of the primary tools in a hacker’s arsenal, with 53% of malware-related ads focused on sales. In 19% of all posts, infostealers designed to steal data are offered. Crypters and code obfuscation tools, used to help attackers hide malware from security tools, are featured in 17% of cases. Additionally, loaders are mentioned in 16% of ads. The median cost of these types of malware stands at $400, $70, and $500, respectively. The most expensive malware is ransomware: its median cost is $7,500, with some offers reaching up to $320,000. Ransomware is primarily distributed through affiliate programs, known as Ransomware-as-a-Service (RaaS), where participants in an attack typically receive 70–90% of the ransom. To become a partner, a criminal must make a contribution of 0.05 Bitcoin (approximately $5,000) and have a solid reputation on the dark web.
Another popular attack tool is exploits: 69% of exploit-related ads focus on sales, with zero-day vulnerability posts accounting for 32% of them. In 31% of cases, the cost of exploits exceeds $20,000 and can reach several million dollars. Access to corporate networks is relatively inexpensive, with 72% of such ads focused on sales, and 62% of them priced at under a thousand dollars. Among cybercriminal services, hacks are the most popular option, accounting for 49% of reports. For example, the price for compromising a personal email account starts at $100, while the cost for a corporate account begins at $200.
Dmitry Streltsov, Threat Analyst at Positive Technologies, says, “On dark web marketplaces, prices are typically determined in one of two ways: either sellers set a fixed price, or auctions are held. Auctions are often used for exclusive items, such as zero-day exploits. The platforms facilitating these deals also generate revenue, often through their own escrow services, which hold the buyer’s funds temporarily until the product or service is confirmed as delivered. On many platforms, these escrow services are managed by either administrators or trusted users with strong reputations. In return, they earn at least 4% of the transaction amount, with the forums setting the rates.”
Considering the cost of tools and services on the dark web, along with the median ransom amount, cybercriminals can achieve a net profit of $100,000–$130,000 from a successful attack—five times the cost of their preparation. For a company, such an incident can result not only in ransom costs but also in massive financial losses due to disrupted business processes. For example, in 2024, due to a ransomware attack, servers of CDK Global were down for two weeks. The company paid cybercriminals $25 million, while the financial losses of dealers due to system downtime exceeded $600 million.
Expert Speak
What the Bybit Hack Reveals About the Future of Crypto Security

Written by Oded Vanunu, Chief Technologist & Head of Product Vulnerability Research at Check Point (more…)
-

 GISEC1 week ago
GISEC1 week agoPositive Technologies @ GISEC Global 2025: Demonstrating Cutting-Edge Cyber Threats and AI Defense Strategies
-

 Cyber Security1 week ago
Cyber Security1 week agoAxis Communications Sheds Light on Video Surveillance Industry Perspectives on AI
-

 GISEC1 week ago
GISEC1 week agoVideo: SANS Institute Weighs in on Deepfakes, Model Poisoning and Risk Frameworks at GISEC Global 2025
-

 GISEC1 week ago
GISEC1 week agoManageEngine @ GISEC Global 2025: AI, Quantum Computing, and Ransomware Form Part of Cybersecurity Outlook for 2025
-

 GISEC1 week ago
GISEC1 week agoVideo: SentinelOne Speaks Hyperautomation, Purple AI, and the Future of Threat Detection at GISEC Global 2025
-

 Africa Focus6 days ago
Africa Focus6 days agoCyberKnight Sets Up South Africa Entity
-

 GISEC1 week ago
GISEC1 week agoGroup-IB @ GISEC Global 2025: Tackling Evolving Cyber Threats with Localised Intelligence and AI
-

 GISEC1 week ago
GISEC1 week agoVideo: CyberKnight on Zero Trust, AI, and Saudi Arabia’s Digital Transformation at GISEC Global 2025






















