Expert Speak
Advanced Cyberthreats Targeting Holiday Shoppers, Says Fortinet

By Derek Manky, Chief Security Strategist and Global VP Threat Intelligence | Board Advisor | Threat Alliances at FortiGuard Labs
As the holiday season approaches, shoppers worldwide eagerly anticipate snagging deals during Black Friday, Cyber Monday, and other holiday sales. However, this heightened online activity also draws the attention of cybercriminals.
A recent report from FortiGuard Labs, Understanding Threat Actor Readiness for the Upcoming Holiday Season, reveals the advanced tactics attackers have been developing to exploit this year’s shopping frenzy. This blog highlights the report’s key findings from the darknet and offers some practical advice to help shoppers and businesses stay secure this season.
The Cyberthreat Landscape
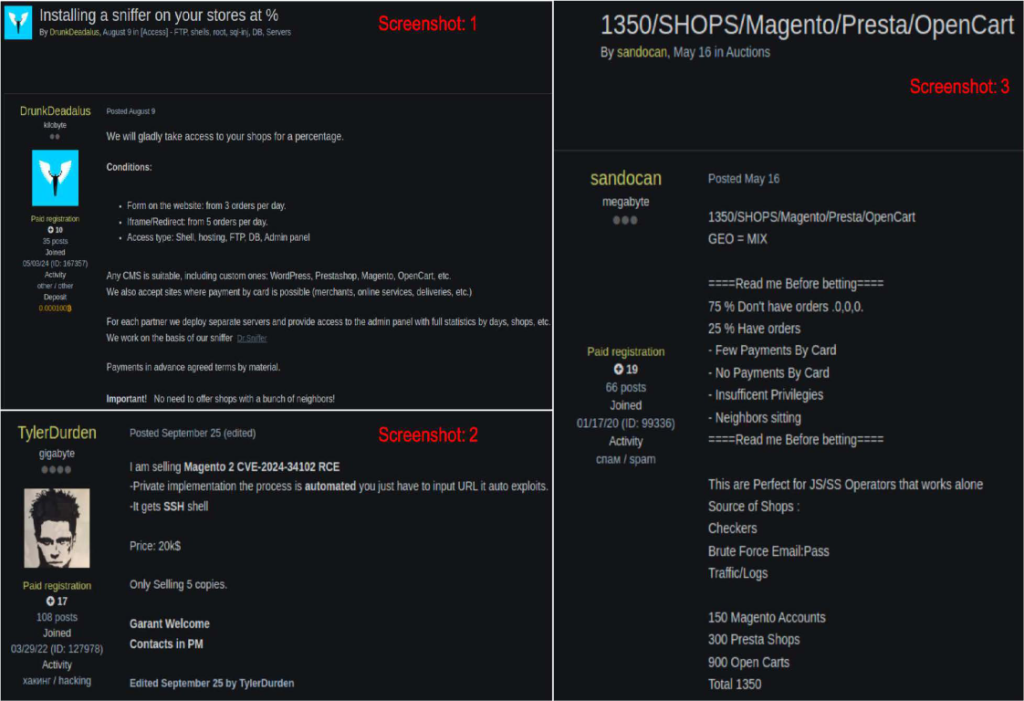
The holiday season presents an irresistible opportunity for cybercriminals to capitalize on increased online transactions. Tools and services now available on the darknet empower attackers to target e-commerce platforms and unsuspecting shoppers more effectively than ever. This year, threat actors are leveraging cutting-edge techniques, including AI-powered phishing lures, sophisticated website cloning tools, and remote code execution (RCE) exploits to gain unauthorized access to shopping platforms. AI-driven methods allow attackers to craft convincing emails and replicas of legitimate websites to steal data or trick users into disclosing sensitive information.
The report also highlights the growing use of deceptive holiday-themed domains that mimic trusted retailers to lure shoppers with enticing but fraudulent offers. Sniffing tools are another critical weapon that enables cybercriminals to intercept sensitive data like credit card details during online transactions. Key highlights from the report include:
- Shopping-themed phishing lures use generative AI. The report includes examples of cybercriminals using AI models like ChatGPT to craft convincing phishing emails, mimicking legitimate communications from retailers and banks. This increases the effectiveness of their scams, especially during peak shopping periods.
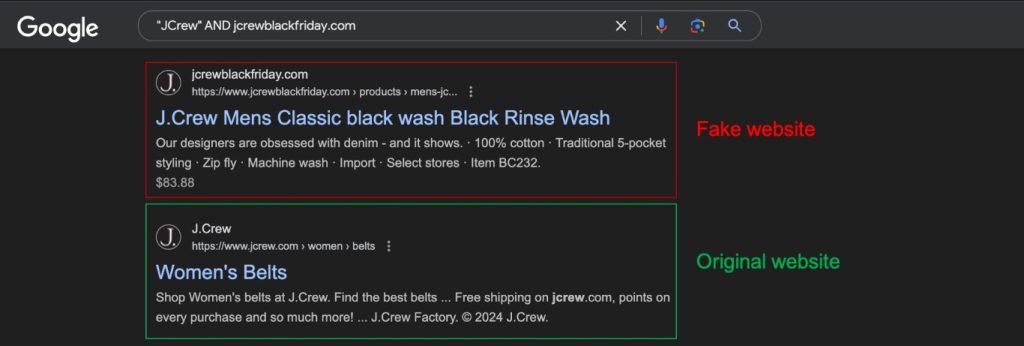
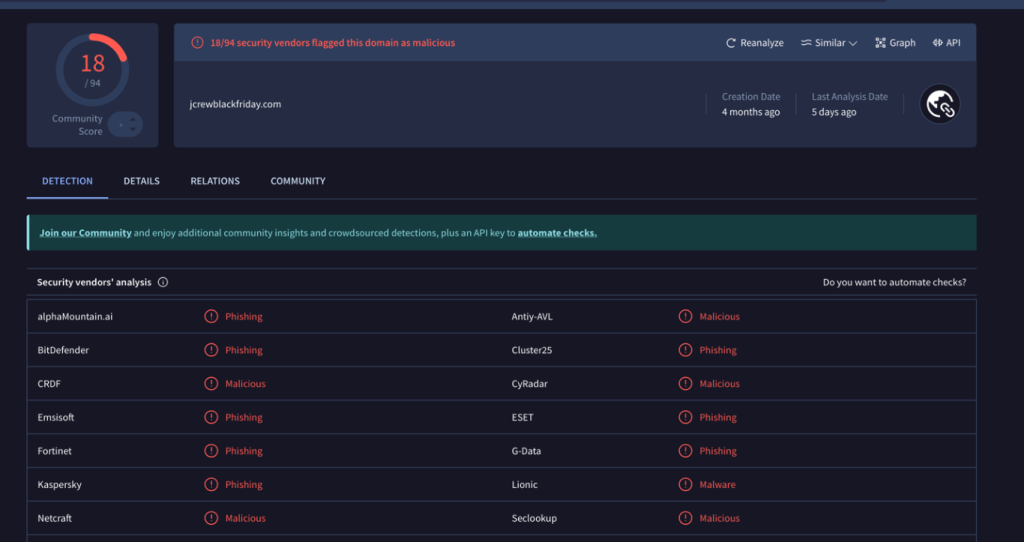
- E-commerce threats abound this holiday season. Threat actors are ramping up efforts to exploit online shopping trends. This year’s report notes that thousands of holiday-themed domains mimicking trusted brands like Amazon and Walmart are being registered to deceive consumers with fake offers and promotions. Popular platforms such as Adobe Commerce, Shopify, and WooCommerce are prime targets due to weak configurations and outdated plugins. Attackers are deploying sniffers to capture customer data and using RCE exploits to gain admin access to shopping platforms.
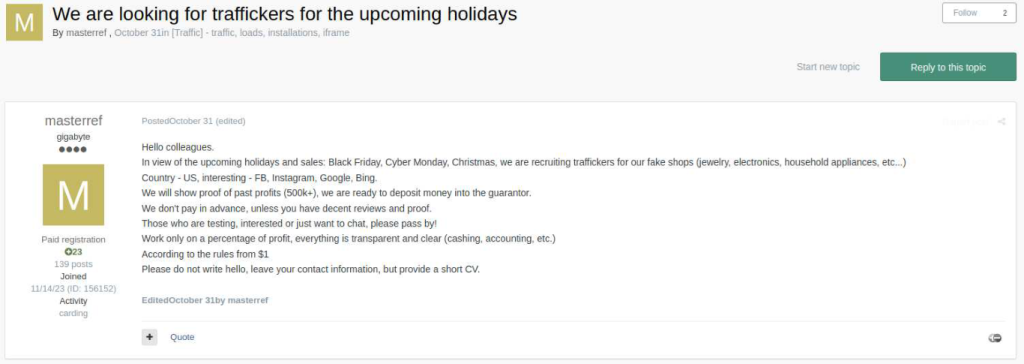
- A multitude of lucrative darknet services fuels cybercrime. The FortiGuard Labs team has observed a surge in the sale of stolen gift cards, credit card data, and compromised e-commerce site databases. Phishing kits enabling attackers to set up advanced phishing operations, including services, are being sold for between $100 and $1,000, depending on complexity and customizations. Other services, such as sniffing and custom brute-forcing tools, are also readily available, enabling even low-skilled attackers to exploit vulnerabilities.
- Rising risks for businesses. Businesses are equally vulnerable, facing significant risks from phishing scams to the theft of financial information through fake websites. Compromised admin panels, unpatched software, and weak credentials can lead to data breaches, fraudulent transactions, and damaged reputations.
Staying Safe This Holiday Season
To mitigate these risks, shoppers and businesses must adopt proactive measures. Vigilance is essential for shoppers. Double-check URLs before entering sensitive information and use secure payment methods such as credit cards with fraud protection. Avoid shopping over public Wi-Fi networks, which can leave you vulnerable to session hijacking. Enabling multi-factor authentication on your accounts can provide an additional layer of security. It is also crucial to monitor your financial statements regularly for unauthorized transactions.
Businesses must prioritize their cybersecurity posture. Keeping e-commerce platforms and plugins up to date and conducting regular vulnerability scans can significantly reduce risk. Implementing advanced fraud detection tools helps identify unusual activities, such as brute-force login attempts or fake traffic. Educating customers on recognizing phishing attempts and promoting safe shopping habits is equally important. Monitoring domain registrations for potential impersonations and reporting them promptly can help protect your brand. Finally, securing admin panels with strong passwords and restricted access can prevent unauthorized breaches.
A Call to Action
The holiday season should be a time of joy and celebration, not risk and vulnerability. However, for this to happen, businesses must take a proactive stance on cybersecurity while consumers must stay informed and cautious about the threats lurking online.
Artificial Intelligence
How AI is Reinventing Cybersecurity for the Automotive Industry

Written by Alain Penel, VP of Middle East, CIS & Turkey at Fortinet (more…)
Cyber Security
Positive Technologies Study Reveals Successful Cyberattacks Nett 5X Profits

Positive Technologies has released a study on the dark web market, analysing prices for illegal cybersecurity services and products, as well as the costs incurred by cybercriminals to carry out attacks. The most expensive type of malware is ransomware, with a median cost of $7,500. Zero-day exploits are particularly valuable, often being sold for millions of dollars. However, the net profit from a successful cyberattack can be five times the cost of organizing it.
Experts estimate that performing a popular phishing attack involving ransomware costs novice cybercriminals at least $20,000. First, hackers rent dedicated servers, subscribe to VPN services, and acquire other tools to build a secure and anonymous IT infrastructure to manage the attack. Attackers also need to acquire the source code of malicious software or subscribe to ready-to-use malware, as well as tools for infiltrating the victim’s system and evading detection by security measures. Moreover, cybercriminals can consult with seasoned experts, purchase access to targeted infrastructures and company data, and escalate privileges within a compromised system. Products and tools are readily available for purchase on the dark web, catering to beginners. The darknet also offers leaked malware along with detailed instructions, making it easier for novice cybercriminals to carry out attacks.
Malware is one of the primary tools in a hacker’s arsenal, with 53% of malware-related ads focused on sales. In 19% of all posts, infostealers designed to steal data are offered. Crypters and code obfuscation tools, used to help attackers hide malware from security tools, are featured in 17% of cases. Additionally, loaders are mentioned in 16% of ads. The median cost of these types of malware stands at $400, $70, and $500, respectively. The most expensive malware is ransomware: its median cost is $7,500, with some offers reaching up to $320,000. Ransomware is primarily distributed through affiliate programs, known as Ransomware-as-a-Service (RaaS), where participants in an attack typically receive 70–90% of the ransom. To become a partner, a criminal must make a contribution of 0.05 Bitcoin (approximately $5,000) and have a solid reputation on the dark web.
Another popular attack tool is exploits: 69% of exploit-related ads focus on sales, with zero-day vulnerability posts accounting for 32% of them. In 31% of cases, the cost of exploits exceeds $20,000 and can reach several million dollars. Access to corporate networks is relatively inexpensive, with 72% of such ads focused on sales, and 62% of them priced at under a thousand dollars. Among cybercriminal services, hacks are the most popular option, accounting for 49% of reports. For example, the price for compromising a personal email account starts at $100, while the cost for a corporate account begins at $200.
Dmitry Streltsov, Threat Analyst at Positive Technologies, says, “On dark web marketplaces, prices are typically determined in one of two ways: either sellers set a fixed price, or auctions are held. Auctions are often used for exclusive items, such as zero-day exploits. The platforms facilitating these deals also generate revenue, often through their own escrow services, which hold the buyer’s funds temporarily until the product or service is confirmed as delivered. On many platforms, these escrow services are managed by either administrators or trusted users with strong reputations. In return, they earn at least 4% of the transaction amount, with the forums setting the rates.”
Considering the cost of tools and services on the dark web, along with the median ransom amount, cybercriminals can achieve a net profit of $100,000–$130,000 from a successful attack—five times the cost of their preparation. For a company, such an incident can result not only in ransom costs but also in massive financial losses due to disrupted business processes. For example, in 2024, due to a ransomware attack, servers of CDK Global were down for two weeks. The company paid cybercriminals $25 million, while the financial losses of dealers due to system downtime exceeded $600 million.
Expert Speak
What the Bybit Hack Reveals About the Future of Crypto Security

Written by Oded Vanunu, Chief Technologist & Head of Product Vulnerability Research at Check Point (more…)
-

 GISEC1 week ago
GISEC1 week agoPositive Technologies @ GISEC Global 2025: Demonstrating Cutting-Edge Cyber Threats and AI Defense Strategies
-

 Cyber Security1 week ago
Cyber Security1 week agoAxis Communications Sheds Light on Video Surveillance Industry Perspectives on AI
-

 GISEC1 week ago
GISEC1 week agoVideo: SANS Institute Weighs in on Deepfakes, Model Poisoning and Risk Frameworks at GISEC Global 2025
-

 GISEC1 week ago
GISEC1 week agoManageEngine @ GISEC Global 2025: AI, Quantum Computing, and Ransomware Form Part of Cybersecurity Outlook for 2025
-

 GISEC1 week ago
GISEC1 week agoVideo: SentinelOne Speaks Hyperautomation, Purple AI, and the Future of Threat Detection at GISEC Global 2025
-

 Africa Focus6 days ago
Africa Focus6 days agoCyberKnight Sets Up South Africa Entity
-

 GISEC1 week ago
GISEC1 week agoGroup-IB @ GISEC Global 2025: Tackling Evolving Cyber Threats with Localised Intelligence and AI
-

 GISEC1 week ago
GISEC1 week agoVideo: CyberKnight on Zero Trust, AI, and Saudi Arabia’s Digital Transformation at GISEC Global 2025




















