News
Canon Intros the CR-N100 4K PTZ Camera and RC-IP1000 Professional PTZ Controller

Canon has announced the CR-N100 indoor 4K pan-tilt-zoom camera – the sixth model in the PTZ lineup designed to achieve high-quality video capture and seamless integration into a multi-camera system. In addition to the latest camera release, Canon introduces the RC-IP1000 professional PTZ controller for broadcast and live events. Canon also launched its new Multi-camera Management Application to facilitate the management workflow of multiple PTZ cameras.
With the addition of the CR-N100 to Canon’s lineup of remote cameras, customers now have a greater choice of products that support a wide range of uses, from professional video production to video content used by enterprises, local governments, and educational institutions.
CR-N100
The CR-N100 excels in image quality, offering unparalleled versatility and performance for its price point. The camera is equipped with a 1/2.3-type 4K CMOS sensor and DIGIC DV6 processor and a powerful optical zoom lens of 20x, delivering crystal-clear 4K UHD resolution footage with exceptional detail and oversampled HD video. As online meetings, lectures, events, and seminars become increasingly commonplace, there is a growing need for live streaming and video recording technology.
The CR-N100 camera includes four different ‘scene modes’ – Portrait, Sports, Low-light and Spotlight – which users can choose to create the best possible visual expression based on their subject. The Hybrid Auto Focus system combines contrast AF with external phase-detection AF, delivering rapid and accurate focusing of the subject even in low light conditions, assisting the camera operator.

The CR-N100 is compatible with Canon’s Auto Tracking App1 as an add-on application offering unparalleled flexibility, enabling the camera to automatically track the main speaker, without the intervention of a camera operator. The camera also supports the Multi-camera Management App that enables batch setting configuration, management and monitoring of up to 200 cameras, making possible efficient operation of large-scale systems in such environments as enterprises, local governments, and educational institutions. These features, combined with the price point of the camera, deliver a budget-friendly but high-quality automated solution.
CR-N100 key features:
- 4K30P high-image-quality video capture
- 20x optical zoom lens with a focal length of 29.3m – 601mm (35mm film equivalent)
- Hybrid Auto Focus with face detection and tracking
- Intelligent Auto Tracking
- In-built protocol support, including Canon XC2, RTMP3/RTMPS and RTP/RTSP, NDI|HX4 and SRT5, making the CR-N100 extremely flexible out of the box
- Compatible HDMI and USB-C connectivity
- Includes additional support tools such as Camera Search Tool, Remote Camera Control Application, and Webcam Driver
RC-IP1000
The RC-IP1000 is a powerful professional broadcast PTZ controller with a host of features aimed to capture every moment with the utmost precision – perfect for busy studios and production teams.
The controller has been designed to perfectly complement Canon’s high-end PTZ models for the broadcast market and is compatible with both IP and serial communication to access and control PTZ cameras remotely. The input monitoring feature enables users to view their feeds on the 7-inch LCD screen, built on the controller, without the need to connect to an external monitor.
The launch of this controller is a direct response to broadcasters’ demands and sports a professional control interface for comfort, paired with a high-quality ergonomic joystick. The RC-IP1000 also features a large touchscreen LCD which enables the user to intuitively access multiple camera settings and features including setting the focus point for cameras. With unrivalled control and no requirement for a PC, this professional PTZ controller has 12G-SDI and HDMI input/outputs up to 4K 60P, enabling the operation and monitoring of up to 200 cameras via IP.
RC-IP1000 key features:
- IP video and input monitoring (up to 200 cameras)
- PC-less setup of cameras from RC-IP1000
- HDMI Out, 12G-SDI in/out, Serial RJ45, LAN/POE+, two USB ports and two GPIO D-Sub 25pin channels
- 7-inch multi-function touchscreen LCD
- Ergonomic joystick and zoom rocker for precise control
- Multiple camera control function – group cameras and apply the same settings
- Arrow buttons for easy menu navigation
- Advanced pre-set and trace control – control other cameras during trace
Matthew Koshy, Product Marketing at Canon Europe, said, “This new line-up represents a seamless blend of innovation and versatility, expanding the offering and empowering users to unlock a whole new world of dynamic control and precision in their visuals. With the CR-N100’s fluid movement and unrivalled image quality for the price point, we have aimed to create a product that widens the range selection available to corporate and education sectors. Meanwhile, our RC-IP1000 controller provides the ultimate professional workflow, pushing live productions to unprecedented heights of excellence.”
Cyber Security
Positive Technologies Reports 80% of Middle East Cyberattacks Compromise Confidential Data

A new study by cybersecurity firm Positive Technologies has shed light on the evolving cyber threat landscape in the Middle East, revealing that a staggering 80% of successful cyberattacks in the region lead to the breach of confidential information. The research, examining the impact of digital transformation, organized cybercrime, and the underground market, highlights the increasing exposure of Middle Eastern nations to sophisticated cyber threats.
The study found that one in three successful cyberattacks were attributed to Advanced Persistent Threat (APT) groups, which predominantly target government institutions and critical infrastructure. While the rapid adoption of new IT solutions is driving efficiency, it simultaneously expands the attack surface for malicious actors.
Cybercriminals in the region heavily utilize social engineering tactics (61% of cases) and malware (51%), often employing a combination of both. Remote Access Trojans (RATs) emerged as a primary weapon in 27% of malware-based attacks, indicating a common objective of gaining long-term access to compromised systems.
The analysis revealed that credentials and trade secrets (29% each) were the most sought-after data, followed by personal information (20%). This stolen data is frequently leveraged for blackmail or sold on the dark web. Beyond data theft, 38% of attacks resulted in the disruption of core business operations, posing significant risks to critical sectors like healthcare, transportation, and government services.
APT groups are identified as the most formidable threat actors due to their substantial resources and advanced technical capabilities. In 2024, they accounted for 32% of recorded attacks, with a clear focus on government and critical infrastructure. Their activities often extend beyond traditional cybercrime, encompassing cyberespionage and even cyberwarfare aimed at undermining trust and demonstrating digital dominance.
Dark web analysis further revealed that government organizations were the most frequently mentioned targets (34%), followed by the industrial sector (20%). Hacktivist activity was also prominent, with ideologically motivated actors often sharing stolen databases freely, exacerbating the cybercrime landscape.
The United Arab Emirates, Saudi Arabia, Israel, and Qatar, all leaders in digital transformation, were the most frequently cited countries on the dark web in connection with stolen data. Experts suggest that the prevalence of advertisements for selling data from these nations underscores the challenges of securing rapidly expanding digital environments, which cybercriminals are quick to exploit.
Positive Technologies analyst Alexey Lukash said, “In the near future, we expect cyberthreats in the Middle East to grow both in scale and sophistication. As digital transformation efforts expand, so does the attack surface, creating more opportunities for hackers of all skill levels. Governments in the region need to focus on protecting critical infrastructure, financial institutions, and government systems. The consequences of successful attacks in these areas could have far-reaching implications for national security and sovereignty.”
To help organizations build stronger defenses against cyberthreats, Positive Technologies recommends implementing modern security measures. These include vulnerability management systems to automate asset management, as well as identify, prioritize, and remediate vulnerabilities. Positive Technologies also suggests using network traffic analysis tools to monitor network activity and detect cyberattacks. Another critical layer of protection involves securing applications. Such solutions are designed to identify vulnerabilities in applications, detect suspicious activity, and take immediate action to prevent attacks.
Positive Technologies emphasizes the need for a comprehensive, result-driven approach to cybersecurity. This strategy is designed to prevent attackers from disrupting critical business processes. Scalable and flexible, it can be tailored to individual organizations, entire industries, or even large-scale digital ecosystems like nations or international alliances. The goal is to deliver clear, measurable results in cybersecurity—not just to meet compliance standards or rely on isolated technical fixes.
Channel Talk
Qualys Partners with Teksalah, the First Middle Eastern MSP in its mROC Alliance

Qualys has announced the expansion of its invite-only managed Risk Operations Center (mROC) Partner Alliance with seven new global partners, including Teksalah from the Middle East. This marks a significant step forward in Qualys’ mission to build a robust Risk Operations Center (ROC) ecosystem—making business-aligned cyber risk management more accessible, actionable, and measurable for organizations worldwide.
Built on the Qualys Enterprise TruRisk™ Management Platform, the ROC framework consolidates risk signals across an organization’s digital footprint into a single pane of glass. It enables Continuous Threat Exposure Management (CTEM), cyber risk quantification, and risk remediation, empowering CISOs to translate cyber risk into business terms, ensure audit readiness, and build long-term resilience.
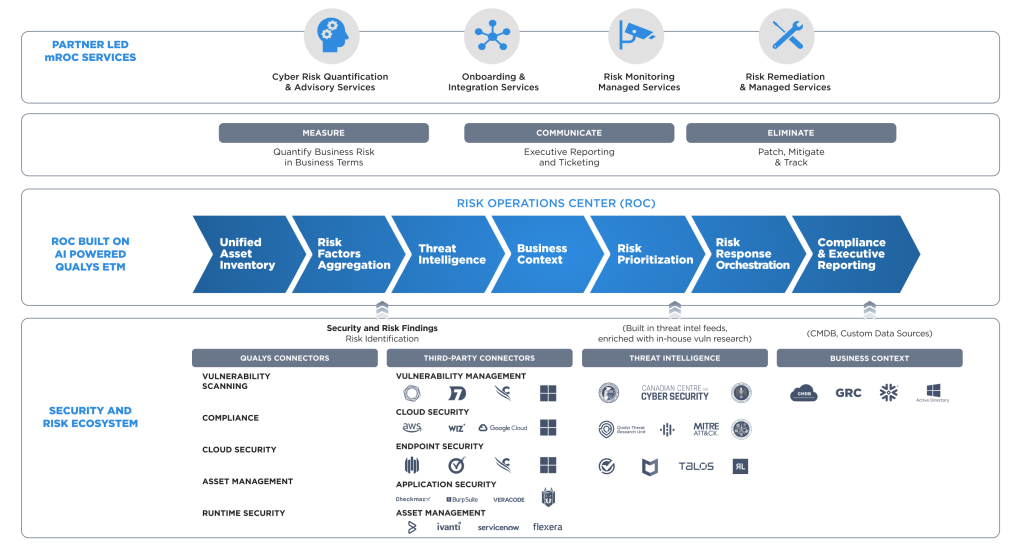
The mROC Partner Alliance equips partners to drive growth by delivering enhanced Qualys-powered ROC services that transform how enterprises measure, manage, and reduce cyber risk. The expanded roster of partners brings world-class expertise to help organizations overcome common cybersecurity challenges such as fragmented tools, disjointed risk response, and limited visibility—enabling a proactive approach to managing cyber risk at scale.
“When we introduced the concept of the Risk Operations Center, we knew it had the potential to redefine how organizations manage cyber risk,” said Sumedh Thakar, president and CEO of Qualys. “Today, with the launch of our inaugural global mROC partners, we’re delivering on that vision. This is a major milestone in building a thriving ROC ecosystem—one that helps businesses around the world take control of cyber risk with clarity, speed, and measurable impact.”
mROC Partners, through a comprehensive suite of risk service offerings, play a critical role in Qualys’ mission to make cyber risk management easier to adopt, more practical to implement, and more impactful for organizations globally. This innovative group of mROC partners has been thoroughly trained and enabled to operate a ROC powered by Qualys Enterprise TruRisk Management (ETM), delivering comprehensive managed risk services. By aggregating and analyzing risk signals from both Qualys and third-party tools, they offer their clients a holistic, business-aligned view of their risk exposure.
“The Teksalah and Qualys partnership is built on a shared vision — to embed a holistic risk-based, proactive approach at the core of enterprise cybersecurity. Through our powerful platforms, intelligent tools, and proven services—covering real-time risk monitoring to effective remediation—we are enabling organizations to manage risk with precision and drive secure innovation. Together, we are transforming our client’s cybersecurity from a control function into a catalyst for business growth and resilience,” commented Murali Konasani, CEO, Teksalah.
Africa Focus
CyberKnight Sets Up South Africa Entity

CyberKnight, a prominent regional cybersecurity advisory and value-added distributor, today announced the establishment of its local entity in Johannesburg, South Africa. The company has also appointed Wade Gomes as Country Manager for the SAADC (Southern African Development Community) region. This move underscores CyberKnight’s dedication to supporting the burgeoning Southern African market, where cybersecurity is increasingly becoming a top priority for organisations across various sectors.
“Wade Gomes’ appointment marks an important milestone for CyberKnight in Southern Africa. His deep industry knowledge, decades of experience and leadership will be instrumental as we expand our presence and work closely with our partners and customers,” said Yaadhna Singh Gounden, Regional Director for Sub-Saharan Africa. “Our goal is to enable organisations to navigate the complexities of today’s cybersecurity landscape with confidence, leveraging best-in-class solutions and proven frameworks.”
South Africa’s ongoing digital transformation, coupled with the rising sophistication of cyber threats, has driven a greater emphasis on implementing strong security solutions and adhering to regulatory compliance. The region’s cybersecurity market is characterised by a significant demand for advanced technologies, particularly in areas like cloud security, AI-powered threat detection, and managed security services. As businesses embrace digitalisation, they encounter new vulnerabilities, necessitating scalable and innovative solutions to safeguard sensitive data and ensure uninterrupted operations. The collaborative efforts between government, businesses, and technology providers to bridge skills gaps and strengthen defenses highlight the significant growth potential in the region.
“I’m excited to be part of CyberKnight’s journey in Southern Africa. The region is at a critical point in its cybersecurity evolution, and there’s a real opportunity to make a lasting impact, by combining local expertise with global experience. I’m honored and excited to lead this mission locally, with a goal to transform South Africa into one of CyberKnight’s hubs and a center of excellence, by helping customers stay ahead of threats while maximising the value of their cybersecurity investments,” added Wade Gomes, Country Manager at CyberKnight.
CyberKnight’s establishment in South Africa signifies its complete coverage across the African continent. The company brings its Zero Trust Security philosophy and a portfolio of leading global cybersecurity vendors to assist enterprise and government organisations throughout Africa in managing risk and enhancing resilience as they navigate evolving regulations and threats.
-

 GISEC1 week ago
GISEC1 week agoPositive Technologies @ GISEC Global 2025: Demonstrating Cutting-Edge Cyber Threats and AI Defense Strategies
-

 Cyber Security1 week ago
Cyber Security1 week agoAxis Communications Sheds Light on Video Surveillance Industry Perspectives on AI
-

 GISEC1 week ago
GISEC1 week agoVideo: SANS Institute Weighs in on Deepfakes, Model Poisoning and Risk Frameworks at GISEC Global 2025
-

 GISEC1 week ago
GISEC1 week agoManageEngine @ GISEC Global 2025: AI, Quantum Computing, and Ransomware Form Part of Cybersecurity Outlook for 2025
-

 GISEC1 week ago
GISEC1 week agoVideo: SentinelOne Speaks Hyperautomation, Purple AI, and the Future of Threat Detection at GISEC Global 2025
-

 Africa Focus6 days ago
Africa Focus6 days agoCyberKnight Sets Up South Africa Entity
-

 GISEC1 week ago
GISEC1 week agoGroup-IB @ GISEC Global 2025: Tackling Evolving Cyber Threats with Localised Intelligence and AI
-

 GISEC1 week ago
GISEC1 week agoVideo: CyberKnight on Zero Trust, AI, and Saudi Arabia’s Digital Transformation at GISEC Global 2025












