Cyber Security
HijackLoader Expands Techniques to Improve Defense Evasion

Written by Donato Onofri, Senior Red Team Engineer at CrowdStrike; and Emanuele Calvelli, Threat Research Engineer at CrowdStrike
CrowdStrike researchers have identified a HijackLoader (aka IDAT Loader) sample that employs sophisticated evasion techniques to enhance the complexity of the threat. HijackLoader, an increasingly popular tool among adversaries for deploying additional payloads and tooling, continues to evolve as its developers experiment and enhance its capabilities.
In their analysis of a recent HijackLoader sample, CrowdStrike researchers discovered new techniques designed to increase the defence evasion capabilities of the loader. The malware developer used a standard process hollowing technique coupled with an additional trigger that was activated by the parent process writing to a pipe. This new approach has the potential to make defence evasion stealthier.
The second technique variation involved an uncommon combination of process doppelgänging and process hollowing techniques. This variation increases the complexity of analysis and the defence evasion capabilities of HijackLoader. Researchers also observed additional unhooking techniques used to hide malicious activity.
This blog focuses on the various evasion techniques employed by HijackLoader at multiple stages of the malware.
HijackLoader Analysis
Infection Chain Overview
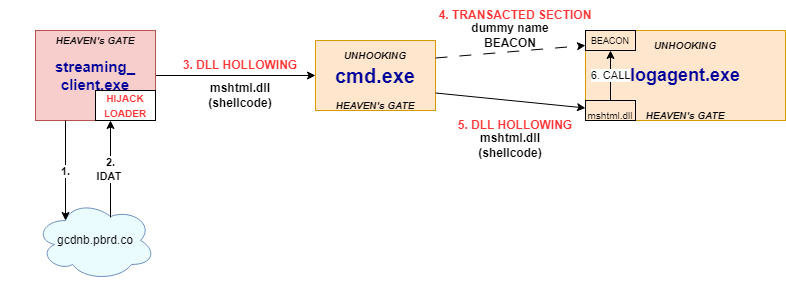
The HijackLoader sample CrowdStrike analyzed implements complex multi-stage behaviour in which the first-stage executable (streaming_client.exe) deobfuscates an embedded configuration partially used for dynamic API resolution (using PEB_LDR_DATA structure without another API usage) to harden against static analysis.
Afterwards, the malware uses WinHTTP APIs to check if the system has an active internet connection by connecting to https[:]//nginx[.]org.
If the initial connectivity check succeeds, then execution continues, and it connects to a remote address to download the second-stage configuration blob. If the first URL indicated below fails, the malware iterates through the following list:
- https[:]//gcdnb[.]pbrd[.]co/images/62DGoPumeB5P.png?o=1
- https[:]//i[.]imgur[.]com/gyMFSuy.png;
- https[:]//bitbucket[.]org/bugga-oma1/sispa/downloads/574327927.png
Upon successfully retrieving the second-stage configuration, the malware iterates over the downloaded buffer, checking for the initial bytes of a PNG header. It then proceeds to search for the magic value C6 A5 79 EA, which precedes the XOR key (32 B3 21 A5 in this sample) used to decrypt the rest of the configuration blob.
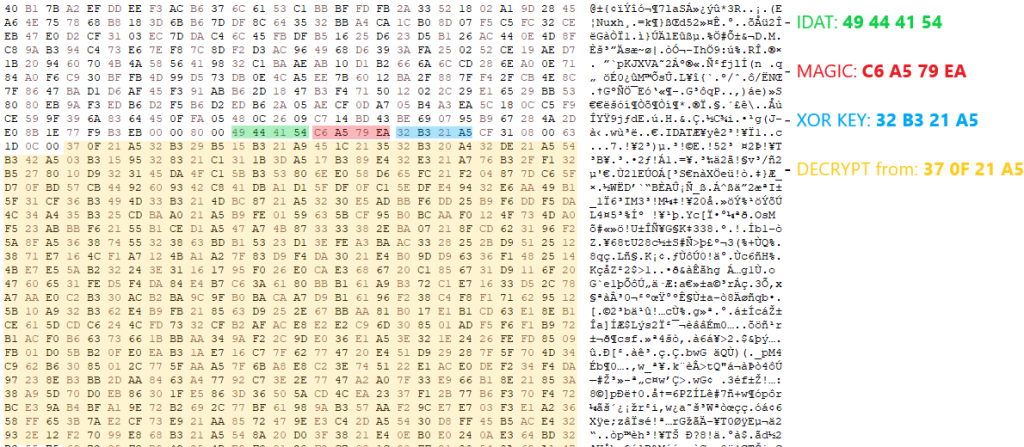
Following XOR decryption, the configuration undergoes decompression using the RtlDecompressBuffer API with COMPRESSION_FORMAT_LZNT1. After decompressing the configuration, the malware loads a legitimate Windows DLL specified in the configuration blob (in this sample, C:\Windows\SysWOW64\mshtml.dll).
The second-stage, position-independent shellcode retrieved from the configuration blob is written to the .text section of the newly loaded DLL before being executed. The HijackLoader second-stage, position-independent shellcode then performs some evasion activities (further detailed below) to bypass user mode hooks using Heaven’s Gate and injects subsequent shellcode into cmd.exe.The injection of the third-stage shellcode is accomplished via a variation of process hollowing that results in an injected hollowed mshtml.dll into the newly spawned cmd.exe child process.
The third-stage shellcode implements a user mode hook bypass before injecting the final payload (a Cobalt Strike beacon for this sample) into the child process logagent.exe. The injection mechanism used by the third-stage shellcode leverages the following techniques:
- Process Doppelgänging Primitives: This technique is used to hollow a Transacted Section(dll) in the remote process to contain the final payload.
- Process/DLL Hollowing: This technique is used to inject the fourth-stage shellcode that is responsible for performing evasion before passing execution to the final payload within the transacted section from the previous step.
The figure below, details the attack path exhibited by this HijackLoader variant.
Main Evasion Techniques Used by HijackLoader and Shellcode
The primary evasion techniques employed by the HijackLoader include hook bypass methods such as Heaven’s Gate and unhooking by remapping system DLLs monitored by security products. Additionally, the malware implements variations of process hollowing and an injection technique that leverages transacted hollowing, which combines the transacted section and process doppelgänging techniques with DLL hollowing.
Like other variants of HijackLoader, this sample implements a user mode hook bypass using Heaven’s Gate (when run in SysWOW64) — this is similar to existing (x64_Syscall function) implementations. This implementation of Heaven’s Gate is a powerful technique that leads to evading user mode hooks placed in SysWOW64 ntdll.dll by directly calling the syscall instruction in the x64 version of ntdll.
Each call to Heaven’s Gate uses the following as arguments:
- The syscall number
- The number of parameters of the syscall
- The parameters (according to the syscall)
This variation of the shellcode incorporates an additional hook bypass mechanism to elude any user mode hooks that security products may have placed in the x64 ntdll. These hooks are typically used for monitoring both the x32 and x64 ntdll. During this stage, the malware remaps the .text section of x64 ntdll by using Heaven’s Gate to call NtWriteVirtualMemory and NtProtectVirtualMemory to replace the in-memory mapped ntdll with the .text from a fresh ntdll read from the file C:\windows\system32\ntdll.dll. This unhooking technique is also used on the process hosting the final Cobalt Strike payload (logagent.exe) in a final attempt to evade detection.
Process Hollowing Variation
To inject the subsequent shellcode into the child process cmd.exe, the malware utilizes common process hollowing techniques. This involves mapping the legitimate Windows DLL mshtml.dll into the target process and then replacing its .text section with shellcode. An additional step necessary to trigger the execution of the remote shellcode is detailed in a later section.
To set up the hollowing, the sample creates two pipes that are used to redirect the Standard Input and the Standard Output of the child process (specified in the aforementioned configuration blob, C:\windows\syswow64\cmd.exe) by placing the pipes’ handles in a STARTUPINFOW structure spawned with CreateProcessW API.
One key distinction between this implementation and the typical “standard” process hollowing can be observed here: In standard process hollowing, the child process is usually created in a suspended state. In this case, the child is not explicitly created in a suspended state, making it appear less suspicious. Since the child process is waiting for an input from the pipe created previously, its execution is hanging on receiving data from it. Essentially, we can call this an interactive process hollowing variation.
As a result, the newly spawned cmd.exe will read input from the STDIN pipe, effectively waiting for new commands. At this point, its EIP (Extended Instruction Pointer) is directed toward the return from the NtReadFile syscall. The following section details the steps taken by the second-stage shellcode to set up the child process cmd.exe ultimately used to perform the subsequent injections used to execute the final payload.
The parent process streaming_client.exe initiates an NtDelayExecution to sleep, waiting for cmd.exe to finish loading. Afterwards, it reads the legitimate Windows DLL mshtml.dll from the file system and proceeds to load this library into cmd.exe as a shared section. This is accomplished using the Heaven’s Gate technique for:
- Creating a shared section object using NtCreateSection
- Mapping that section in the remote exe using NtMapViewOfSection
It then replaces the .text section of the mshtml DLL with malicious shellcode by using:
- Heaven’s Gate to call NtProtectVirtualMemory on exe to set RWX permissions on the .text section of the previously mapped section mshtml.dll
- Heaven’s Gate to call NtWriteVirtualMemoryon the DLL’s .text section to stomp the module and write the third-stage shellcode
Finally, to trigger the execution of the remote-injected shellcode, the malware uses:
- Heaven’s Gate to suspend (NtSuspendThread) the remote main thread
- A new CONTEXT (by using NtGetContextThread and NtSetContextThread) to modify the EIP to point to the previously written shellcode
- Heaven’s Gate to resume (NtResumeThread) the remote main thread of exe
However, because cmd.exe is waiting for user input from the STDINPUT pipe, the injected shellcode in the new process isn’t executed upon the resumption of the thread. The loader must take an additional step:
- The parent process exe needs to write (WriteFile) \r\n string to the STDINPUT pipe created previously to send an input to cmd.exe after calling NtResumeThread. This effectively resumes execution of the primary thread at the shellcode’s entry point in the child process cmd.exe.
Interactive Process Hollowing Variation: Tradecraft Analysis
We have successfully replicated the threadless process hollowing technique to understand how the pipes trigger it. Once the shellcode has been written as described, it needs to be activated. This activation is based on the concept that when a program makes a syscall, the thread waits for the kernel to return a value.
In essence, the interactive process hollowing technique involves the following steps:
- CreateProcess: This step involves spawning the exe process to inject the malicious code by redirecting STDIN and STDOUT to pipes. Notably, this process isn’t suspended, making it appear less suspicious. Waiting to read input from the pipe, the NtReadFile syscall sets its main thread’s state to Waiting and _KWAIT_REASON to Executive, signifying that it’s awaiting the execution of kernel code operations and their return.
- WriteProcessMemory: This is where the shellcode is written into the exe child process.
- SetThreadContext: In this phase, the parent sets the conditions to redirect the execution flow of the exe child process to the previously written shellcode’s address by modifying the EIP/RIP in the remote thread CONTEXT.
- WriteFile: Here, data is written to the STDIN pipe, sending an input to the exe process. This action resumes the execution of the child process from the NtReadFile operation, thus triggering the execution of the shellcode. Before returning to user space, the kernel reads and restores the values saved in the _KTRAP_FRAME structure (containing the EIP/RIP register value) to resume from where the syscall was called. By modifying the CONTEXT in the previous step, the loader hijacks the resuming of the execution toward the shellcode address without the need to suspend and resume the thread, which this technique usually requires.
Transacted Hollowing² (Transacted Section/Doppelgänger + Hollowing)
The malware writes the final payload in the child process logagent.exe spawned by the third-stage shellcode in cmd.exe by creating a transacted section to be mapped in the remote process. Subsequently, the malware injects a fourth-stage shellcode into logagent.exe by loading and hollowing another instance of mshtml.dll into the target process. The injected fourth-stage shellcode performs the aforementioned hook bypass technique before executing the final payload previously allocated by the transacted section.
Transacted Section Hollowing
Similarly to process doppelgänging, the goal of a transacted section is to create a stealthy malicious section inside a remote process by overwriting the memory of the legitimate process with a transaction. In this sample, the third-stage shellcode executed inside cmd.exe places a malicious transacted section used to host the final payload in the target child process logagent.exe. The shellcode uses the following:
- NtCreateTransactionto create a transaction
- RtlSetCurrentTransaction and CreateFileW with a dummy file name to replace the documented CreateFileTransactedW
- Heaven’s Gate to call NtWriteFilein a loop, writing the final shellcode to the file in 1,024-byte chunks
- Creation of a section backed by that file (Heaven’s Gate call NtCreateSection)
- A rollback of the previously created section by using Heaven’s Gate to call NtRollbackTransaction
Existing similar implementations have publicly been observed in this project that implements transaction hollowing.
Once the transacted section has been created, the shellcode generates a function stub at runtime to hide from static analysis. This stub contains a call to theCreateProcessW API to spawn a suspended child process logagent.exe (c50bffbef786eb689358c63fc0585792d174c5e281499f12035afa1ce2ce19c8) that was previously dropped by cmd.exe under the %TEMP% folder.
After the target process has been created, the sample uses Heaven’s Gate to:
- Read its PEBby calling NtReadVirtualMemory to retrieve its base address (0x400000)
- Unmap the exe image in the logagent.exe process by using NtUnMapViewofSection
- Hollow the previously created transacted section inside the remote process by remapping the section at the same base address (0x400000) with NtMapViewofSection
Process Hollowing
After the third-stage shellcode within cmd.exe injects the final Cobalt Strike payload inside the transacted section of the logagent.exe process, it continues by process hollowing the target process to write the fourth shellcode stage ultimately used to execute the final payload (loaded in the transacted section) in the remote process. The third-stage shellcode maps the legitimate Windows DLL C:\Windows\SysWOW64\mshtml.dll in the target process before replacing its .text with the fourth-stage shellcode and executing it via NtResumeThread.
This additional fourth-stage shellcode written to logagent.exe performs similar evasion activities to the third-stage shellcode executed in cmd.exe (as indicated in the hook bypass section) before passing execution to the final payload.
Indicators of Compromise (IOCs)
| File | SHA256 |
| streaming_client.exe | 6f345b9fda1ceb9fe4cf58b33337bb9f820550ba08ae07c782c2e142f7323748 |
MITRE ATT&CK Framework
The following table maps reported HijackLoader tactics, techniques and procedures (TTPs) to the MITRE ATT&CK framework.
| ID | Technique | Description |
| T1204.002 | User Execution: Malicious File | The sample is a backdoored version of streaming_client.exe, with the Entry Point redirected to a malicious stub. |
| T1027.007 | Obfuscated Files or Information: Dynamic API Resolution | HijackLoader and its stages hide some of the important imports from the IAT by dynamically retrieving kernel32 and ntdll API addresses. It does this by parsing PEB->PEB_LDR_DATA and retrieving the function addresses. |
| T1016.001 | System Network Configuration Discovery: Internet Connection Discovery | This variant of HijackLoader connects to a remote server to check if the machine is connected to the internet by using the WinHttp API (WinHttpOpenRequest and WinHttpSendRequest). |
| T1140 | Deobfuscate/Decode Files or Information | HijackLoader utilizes XOR mechanisms to decrypt the downloaded stage. |
| T1140 | Deobfuscate/Decode Files or Information | HijackLoader utilizes RtlDecompressBuffer to LZ decompress the downloaded stage. |
| T1027 | Obfuscated Files or Information | HijackLoader drops XOR encrypted files to the %APPDATA% subfolders to store the downloaded stages. |
| T1620 | Reflective Code Loading
|
HijackLoader reflectively loads the downloaded shellcode in the running process by loading and stomping the mshtml.dll module using the LoadLibraryW and VirtualProtect APIs. |
| T1106 | Native API
|
HijackLoader uses direct syscalls and the following APIs to perform bypasses and injections: WriteFileW, ReadFile, CreateFileW, LoadLibraryW, GetProcAddress, NtDelayExecution, RtlDecompressBuffer, CreateProcessW, GetModuleHandleW, CopyFileW, VirtualProtect, NtProtectVirtualMemory, NtWriteVirtualMemory, NtResumeThread, NtSuspendThread, NtGetContextThread, NtSetContextThread, NtCreateTransaction, RtlSetCurrentTransaction, NtRollbackTransaction, NtCreateSection, NtMapViewOfSection, NtUnMapViewOfSection, NtWriteFile, NtReadFile, NtCreateFile and CreatePipe. |
| T1562.001 | Impair Defenses: Disable or Modify Tools | HijackLoader and its stages use Heaven’s Gate and remap x64 ntdll to bypass user-space hooks. |
| T1055.012 | Process Injection: Process Hollowing | HijackLoader and its stages implement a process hollowing technique variation to inject in cmd.exe and logagent.exe. |
| T1055.013 | Process Injection: Process Doppelgänging | The HijackLoader shellcode implements a process doppelgänging technique variation (transacted section hollowing) to load the final stage in logagent.exe. |
Cyber Security
Positive Technologies Reports 80% of Middle East Cyberattacks Compromise Confidential Data

A new study by cybersecurity firm Positive Technologies has shed light on the evolving cyber threat landscape in the Middle East, revealing that a staggering 80% of successful cyberattacks in the region lead to the breach of confidential information. The research, examining the impact of digital transformation, organized cybercrime, and the underground market, highlights the increasing exposure of Middle Eastern nations to sophisticated cyber threats.
The study found that one in three successful cyberattacks were attributed to Advanced Persistent Threat (APT) groups, which predominantly target government institutions and critical infrastructure. While the rapid adoption of new IT solutions is driving efficiency, it simultaneously expands the attack surface for malicious actors.
Cybercriminals in the region heavily utilize social engineering tactics (61% of cases) and malware (51%), often employing a combination of both. Remote Access Trojans (RATs) emerged as a primary weapon in 27% of malware-based attacks, indicating a common objective of gaining long-term access to compromised systems.
The analysis revealed that credentials and trade secrets (29% each) were the most sought-after data, followed by personal information (20%). This stolen data is frequently leveraged for blackmail or sold on the dark web. Beyond data theft, 38% of attacks resulted in the disruption of core business operations, posing significant risks to critical sectors like healthcare, transportation, and government services.
APT groups are identified as the most formidable threat actors due to their substantial resources and advanced technical capabilities. In 2024, they accounted for 32% of recorded attacks, with a clear focus on government and critical infrastructure. Their activities often extend beyond traditional cybercrime, encompassing cyberespionage and even cyberwarfare aimed at undermining trust and demonstrating digital dominance.
Dark web analysis further revealed that government organizations were the most frequently mentioned targets (34%), followed by the industrial sector (20%). Hacktivist activity was also prominent, with ideologically motivated actors often sharing stolen databases freely, exacerbating the cybercrime landscape.
The United Arab Emirates, Saudi Arabia, Israel, and Qatar, all leaders in digital transformation, were the most frequently cited countries on the dark web in connection with stolen data. Experts suggest that the prevalence of advertisements for selling data from these nations underscores the challenges of securing rapidly expanding digital environments, which cybercriminals are quick to exploit.
Positive Technologies analyst Alexey Lukash said, “In the near future, we expect cyberthreats in the Middle East to grow both in scale and sophistication. As digital transformation efforts expand, so does the attack surface, creating more opportunities for hackers of all skill levels. Governments in the region need to focus on protecting critical infrastructure, financial institutions, and government systems. The consequences of successful attacks in these areas could have far-reaching implications for national security and sovereignty.”
To help organizations build stronger defenses against cyberthreats, Positive Technologies recommends implementing modern security measures. These include vulnerability management systems to automate asset management, as well as identify, prioritize, and remediate vulnerabilities. Positive Technologies also suggests using network traffic analysis tools to monitor network activity and detect cyberattacks. Another critical layer of protection involves securing applications. Such solutions are designed to identify vulnerabilities in applications, detect suspicious activity, and take immediate action to prevent attacks.
Positive Technologies emphasizes the need for a comprehensive, result-driven approach to cybersecurity. This strategy is designed to prevent attackers from disrupting critical business processes. Scalable and flexible, it can be tailored to individual organizations, entire industries, or even large-scale digital ecosystems like nations or international alliances. The goal is to deliver clear, measurable results in cybersecurity—not just to meet compliance standards or rely on isolated technical fixes.
Cyber Security
Axis Communications Sheds Light on Video Surveillance Industry Perspectives on AI

Axis Communications has published a new report that explores the state of AI in the global video surveillance industry. Titled The State of AI in Video Surveillance, the report examines the key opportunities, challenges and future trends, as well as the responsible practices that are becoming critical for organisations in their use of AI. The report draws insights from qualitative research as well as quantitative data sources, including in-depth interviews with carefully selected experts from the Axis global partner network.
A leading insight featured in the report is the unanimous view among interviewees that interest in the technology has surged over the past few years, with more and more business customers becoming curious and increasingly knowledgeable about its potential applications.

Mats Thulin, Director AI & Analytics Solutions at Axis Communications
“AI is a technology that has the potential to touch every corner and every function of the modern enterprise. That said, any implementations or integrations that aim to drive value come with serious financial and ethical considerations. These considerations should prompt organisations to scrutinise any initiative or investment. Axis’s new report not only shows how AI is transforming the video surveillance landscape, but also how that transformation should ideally be approached,” said Mats Thulin, Director AI & Analytics Solutions at Axis Communications.
According to the Axis report, the move by businesses from on-premise security server systems to hybrid cloud architectures continues at pace, driven by the need for faster processing, improved bandwidth usage and greater scalability. At the same time, cloud-based technology is being combined with edge AI solutions, which play a crucial role by enabling faster, local analytics with minimal latency, a prerequisite for real-time responsiveness in security-related situations.
By moving AI processing closer to the source using edge devices such as cameras, businesses can reduce bandwidth consumption and better support real-time applications like security monitoring. As a result, the hybrid approach is expected to continue to shape the role of AI in security and unlock new business intelligence and operational efficiencies.
A trend that is emerging among businesses is the integration of diverse data for a more comprehensive analysis, transforming safety and security. Experts predict that by integrating additional sensory data, such as audio and contextual environmental factors caught on camera, can lead to enhanced situational awareness and greater actionable insights, offering a more comprehensive understanding of events.
Combining multiple data streams can ultimately lead to improved detection and prediction of potential threats or incidents. For example, in emergency scenarios, pairing visual data with audio analysis can enable security teams to respond more quickly and precisely. This context-aware approach can potentially elevate safety, security and operational efficiency, and reflects how system operators can leverage and process multiple data inputs to make better-informed decisions.
According to the Axis report, interviewees emphasised that responsible AI and ethical considerations are critical priorities in the development and deployment of new systems, raising concerns about decisions potentially based on biased or unreliable AI. Other risks highlighted include those related to privacy violations and how facial and behavioural recognition could have ethical and legal repercussions.
As a result, a recurring theme among interviewees was the importance of embedding responsible AI practices early in the development process. Interviewees also pointed to regulatory frameworks, such as the EU AI Act, as pivotal in shaping responsible use of technology, particularly in high-risk areas. While regulation was broadly acknowledged as necessary to build trust and accountability, several interviewees also stressed the need for balance to safeguard innovation and address privacy and data security concerns.
“The findings of this report reflect how enterprises are viewing the trend of AI holistically, working to have a firm grasp of both how to use the technology effectively and understand the macro implications of its usage. Conversations surrounding privacy and responsibility will continue but so will the pace of innovation and the adoption of technologies that advance the video surveillance industry and lead to new and exciting possibilities,” Thulin added.
Artificial Intelligence
CyberKnight Partners with Ridge Security for AI-Powered Security Validation

The automated penetration testing market was valued at roughly $3.1 billion in 2023 and is projected to grow rapidly, with forecasts estimating a compound annual growth rate (CAGR) between 21% and 25%. By 2030, the sector is expected to reach approximately $9 to $10 billion. The broader penetration testing industry is also expanding, with projections indicating it will surpass $5.3 billion by 2027, according to MarketandMarket.
To support enterprises and government entities across the Middle East, Turkey and Africa (META) with identifying and validating vulnerabilities and reducing security gaps in real-time, CyberKnight has partnered with Ridge Security, the World’s First Al-powered Offensive Security Validation Platform. Ridge Security’s products incorporate advanced artificial intelligence to deliver security validation through automated penetration testing and breach and attack simulations.
RidgeBot uses advanced AI to autonomously perform multi-vector iterative attacks, conduct continuous penetration testing, and validate vulnerabilities with zero false positives. RidgeBot has been deployed by customers worldwide as a key element of their journey to evolve from traditional vulnerability management to Continuous Threat Exposure Management (CTEM).
“Ridge Security’s core strength lies in delivering holistic, AI-driven security validation that enables organizations to proactively manage risk and improve operational performance,” said Hom Bahmanyar, Chief Enablement Officer at Ridge Security. “We are delighted to partner with CyberKnight to leverage their network of strategic partners, deep-rooted customer relations, and security expertise to accelerate our expansion plans in the region.”
“Our partnership with Ridge Security is a timely and strategic step, as 69% of organizations are now adopting AI-driven security for threat detection and prevention,” added Wael Jaber, Chief Strategy Officer at CyberKnight. “By joining forces, we enhance our ability to deliver automated, intelligent security validation solutions, reaffirming our commitment to empowering customers with resilient, future-ready cybersecurity across the region.”
-

 GISEC1 week ago
GISEC1 week agoPositive Technologies @ GISEC Global 2025: Demonstrating Cutting-Edge Cyber Threats and AI Defense Strategies
-

 Cyber Security1 week ago
Cyber Security1 week agoAxis Communications Sheds Light on Video Surveillance Industry Perspectives on AI
-

 GISEC1 week ago
GISEC1 week agoVideo: SANS Institute Weighs in on Deepfakes, Model Poisoning and Risk Frameworks at GISEC Global 2025
-

 GISEC1 week ago
GISEC1 week agoManageEngine @ GISEC Global 2025: AI, Quantum Computing, and Ransomware Form Part of Cybersecurity Outlook for 2025
-

 GISEC1 week ago
GISEC1 week agoVideo: SentinelOne Speaks Hyperautomation, Purple AI, and the Future of Threat Detection at GISEC Global 2025
-

 Africa Focus6 days ago
Africa Focus6 days agoCyberKnight Sets Up South Africa Entity
-

 GISEC1 week ago
GISEC1 week agoGroup-IB @ GISEC Global 2025: Tackling Evolving Cyber Threats with Localised Intelligence and AI
-

 GISEC1 week ago
GISEC1 week agoVideo: CyberKnight on Zero Trust, AI, and Saudi Arabia’s Digital Transformation at GISEC Global 2025










