Expert Speak
Seven Trends That Can Help Make the Modern Enterprise More Secure and Agile

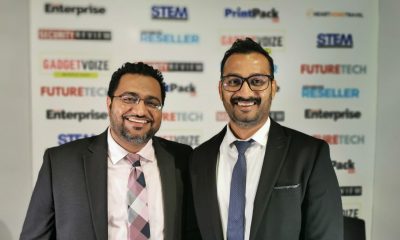
Sajith Kumar, General Manager – Enterprise from Cloud Box Technologies summarizes possible technology and strategic measures in 2022 that can help transform security for the enterprise.
For the Boards of global and regional organizations, cybersecurity and managing digital transformation alongside, are promising to be amongst the most challenging. While Boards are doing a lot to bridge the gap between themselves and the CISO and the security organization, here are some other technology and strategic measures that can help make the enterprise more agile and secure.
Trend #1 The big policy reset
What is the biggest and most immediate change required in an organization’s security policies? It is the fact that majority of its employees are no longer employees but more like remote workers. Or in other words, remote workers are now the workers and remote work is now the organization’s work. In other words, enterprises need to reset their entire security policies and tools to be able to manage risks from this new organizational reality.
Trend #2 Managing workers
How will security be deployed for the modern hybrid organization, where workers are switching between multiple modes of working. At times they will be onsite inside the office firewall, at other times mobile and on the move, and at other times working from home. All the while accessing the wireless networks, Internet or private VPNs. How will an organization’s security architecture continuously adjust for its workers as they move across its fabric?
Today’s enterprises are being turned inside out with these challenges of managing workers requiring multiple modes and levels of security access. All organizations will need to have a defensive posture and well-defined security policies and risks with regard to onsite, remote, and mobile workers. One of the approaches is to develop and deploy a cybersecurity mesh, which enables a distributed enterprise to deploy and extend security where it is required the most.
Trend #3 Managing enterprise assets
Other than the pandemic, digital transformation is also responsible for connecting industrial, operational, IT assets that are distributed across the fabric of the organization. These assets could be located at the edge, inside the network, at the core, and even inside other networks.
Gateways and middleware are now effectively and efficiently connecting disparate networks inside enterprises that were not feasible a decade ago. To manage all these challenges, security needs to be flexible, agile, scalable and yet robust enough to deliver for workers and protect for the organization.
Trend #4 Just who is an employee?
As workers move across the enterprises’ security fabric, their security access levels need to keep changing. More importantly so should their identity-based security, with zero-trust being a dominant requirement. While zero-trust identity access is not new, it gains renewed importance in the face of hybrid worker access as well integration of disparate networks driven by digital transformation.
Social engineering to gain identity access is a dominant activity for sophisticated global threat actors. Hence, identity management techniques and practices need to be further elevated in terms of importance. Along with human identities, we also have machine and robot identities, that are adding additional complexities in the overall identity access management operations.
Digital technologies such as robotic process automation are driving automation of processes and each of these automated process or Bots requires a sign-on into the network and application stacks. APIs are another vulnerable hot spot where access is granted to users across multiple applications via APIs. To better manage digital transformation, enterprises need to relook at their end-to-end identity credentials across all humans, Bots, devices.
Trend #5 Board improves communication
Boards are now alerted to address the challenges thrown up by ransomware, advanced persistent threats, and other supply chain malware that are having disastrous effects on some global businesses. Board members have been in the spotlight for being unable to speak the same language as CISOs and therefore unable to bridge the gaps from top to bottom. Now they are forming dedicated committees headed by security experts and selected board members to bridge the gap and address the challenge.
With this initiative, CISOs can expect much better information flow with the Board, as well as much deeper conversations about security spending, policies, proactiveness, risks and governance, strategy.
Trend #6 Proliferation of vendors
An ongoing challenge that continues into the next year is the complexity of security tools that are being managed by CISOs and IT managers. Global surveys by research firm Gartner have found that 78% of CISOs are managing 16 or more tools across their cybersecurity vendor portfolio. While 12% of CISOs are managing more than 46 tools.
The harsh reality is that cybersecurity organisations have far too many tools, from far too many vendors, leading to complex management routines, continuously high demand on skills, and increasing security headcount.
Under these circumstances, CISOs need to begin extended vendor consolidation activities, realising that such activities take time and there is no short-term solution while heading in this direction. Another reality check is that reduction of capex spending may not be a direct, realisable benefit, but rather reduction of indirect costs and increase in operational efficiency are more achievable and realisable targets.
Trend #7 Testing and validation
New tools are being added to the portfolio of solutions that can be used to validate an organization’s security vulnerabilities. One such area is breach and attack simulations that do continuous testing and validation of security controls and test the ability to withstand external threats. It also highlights risks to high-value assets such as highly confidential data.
Another area that is developing is the ability to protect data while it is being read and used, in comparison to protecting data in motion or at rest. This enhanced security allows secure data processing, secure sharing, and cross-border transfers without risks.
Artificial Intelligence
How AI is Reinventing Cybersecurity for the Automotive Industry

Written by Alain Penel, VP of Middle East, CIS & Turkey at Fortinet (more…)
Cyber Security
Positive Technologies Study Reveals Successful Cyberattacks Nett 5X Profits

Positive Technologies has released a study on the dark web market, analysing prices for illegal cybersecurity services and products, as well as the costs incurred by cybercriminals to carry out attacks. The most expensive type of malware is ransomware, with a median cost of $7,500. Zero-day exploits are particularly valuable, often being sold for millions of dollars. However, the net profit from a successful cyberattack can be five times the cost of organizing it.
Experts estimate that performing a popular phishing attack involving ransomware costs novice cybercriminals at least $20,000. First, hackers rent dedicated servers, subscribe to VPN services, and acquire other tools to build a secure and anonymous IT infrastructure to manage the attack. Attackers also need to acquire the source code of malicious software or subscribe to ready-to-use malware, as well as tools for infiltrating the victim’s system and evading detection by security measures. Moreover, cybercriminals can consult with seasoned experts, purchase access to targeted infrastructures and company data, and escalate privileges within a compromised system. Products and tools are readily available for purchase on the dark web, catering to beginners. The darknet also offers leaked malware along with detailed instructions, making it easier for novice cybercriminals to carry out attacks.
Malware is one of the primary tools in a hacker’s arsenal, with 53% of malware-related ads focused on sales. In 19% of all posts, infostealers designed to steal data are offered. Crypters and code obfuscation tools, used to help attackers hide malware from security tools, are featured in 17% of cases. Additionally, loaders are mentioned in 16% of ads. The median cost of these types of malware stands at $400, $70, and $500, respectively. The most expensive malware is ransomware: its median cost is $7,500, with some offers reaching up to $320,000. Ransomware is primarily distributed through affiliate programs, known as Ransomware-as-a-Service (RaaS), where participants in an attack typically receive 70–90% of the ransom. To become a partner, a criminal must make a contribution of 0.05 Bitcoin (approximately $5,000) and have a solid reputation on the dark web.
Another popular attack tool is exploits: 69% of exploit-related ads focus on sales, with zero-day vulnerability posts accounting for 32% of them. In 31% of cases, the cost of exploits exceeds $20,000 and can reach several million dollars. Access to corporate networks is relatively inexpensive, with 72% of such ads focused on sales, and 62% of them priced at under a thousand dollars. Among cybercriminal services, hacks are the most popular option, accounting for 49% of reports. For example, the price for compromising a personal email account starts at $100, while the cost for a corporate account begins at $200.
Dmitry Streltsov, Threat Analyst at Positive Technologies, says, “On dark web marketplaces, prices are typically determined in one of two ways: either sellers set a fixed price, or auctions are held. Auctions are often used for exclusive items, such as zero-day exploits. The platforms facilitating these deals also generate revenue, often through their own escrow services, which hold the buyer’s funds temporarily until the product or service is confirmed as delivered. On many platforms, these escrow services are managed by either administrators or trusted users with strong reputations. In return, they earn at least 4% of the transaction amount, with the forums setting the rates.”
Considering the cost of tools and services on the dark web, along with the median ransom amount, cybercriminals can achieve a net profit of $100,000–$130,000 from a successful attack—five times the cost of their preparation. For a company, such an incident can result not only in ransom costs but also in massive financial losses due to disrupted business processes. For example, in 2024, due to a ransomware attack, servers of CDK Global were down for two weeks. The company paid cybercriminals $25 million, while the financial losses of dealers due to system downtime exceeded $600 million.
Expert Speak
What the Bybit Hack Reveals About the Future of Crypto Security

Written by Oded Vanunu, Chief Technologist & Head of Product Vulnerability Research at Check Point (more…)
-

 GISEC1 week ago
GISEC1 week agoPositive Technologies @ GISEC Global 2025: Demonstrating Cutting-Edge Cyber Threats and AI Defense Strategies
-

 Cyber Security1 week ago
Cyber Security1 week agoAxis Communications Sheds Light on Video Surveillance Industry Perspectives on AI
-

 GISEC1 week ago
GISEC1 week agoVideo: SANS Institute Weighs in on Deepfakes, Model Poisoning and Risk Frameworks at GISEC Global 2025
-

 GISEC1 week ago
GISEC1 week agoManageEngine @ GISEC Global 2025: AI, Quantum Computing, and Ransomware Form Part of Cybersecurity Outlook for 2025
-

 GISEC1 week ago
GISEC1 week agoVideo: SentinelOne Speaks Hyperautomation, Purple AI, and the Future of Threat Detection at GISEC Global 2025
-

 Africa Focus6 days ago
Africa Focus6 days agoCyberKnight Sets Up South Africa Entity
-

 GISEC1 week ago
GISEC1 week agoGroup-IB @ GISEC Global 2025: Tackling Evolving Cyber Threats with Localised Intelligence and AI
-

 GISEC1 week ago
GISEC1 week agoVideo: CyberKnight on Zero Trust, AI, and Saudi Arabia’s Digital Transformation at GISEC Global 2025